Kubernetes Security That Just Works
Juliet maps your clusters as a security graph, surfacing real attack paths, scanning vulnerabilities, enforcing admission policies, and detecting runtime threats. One CNAPP platform, five-minute setup.
Free tier — no credit card required. Results in 5 minutes.
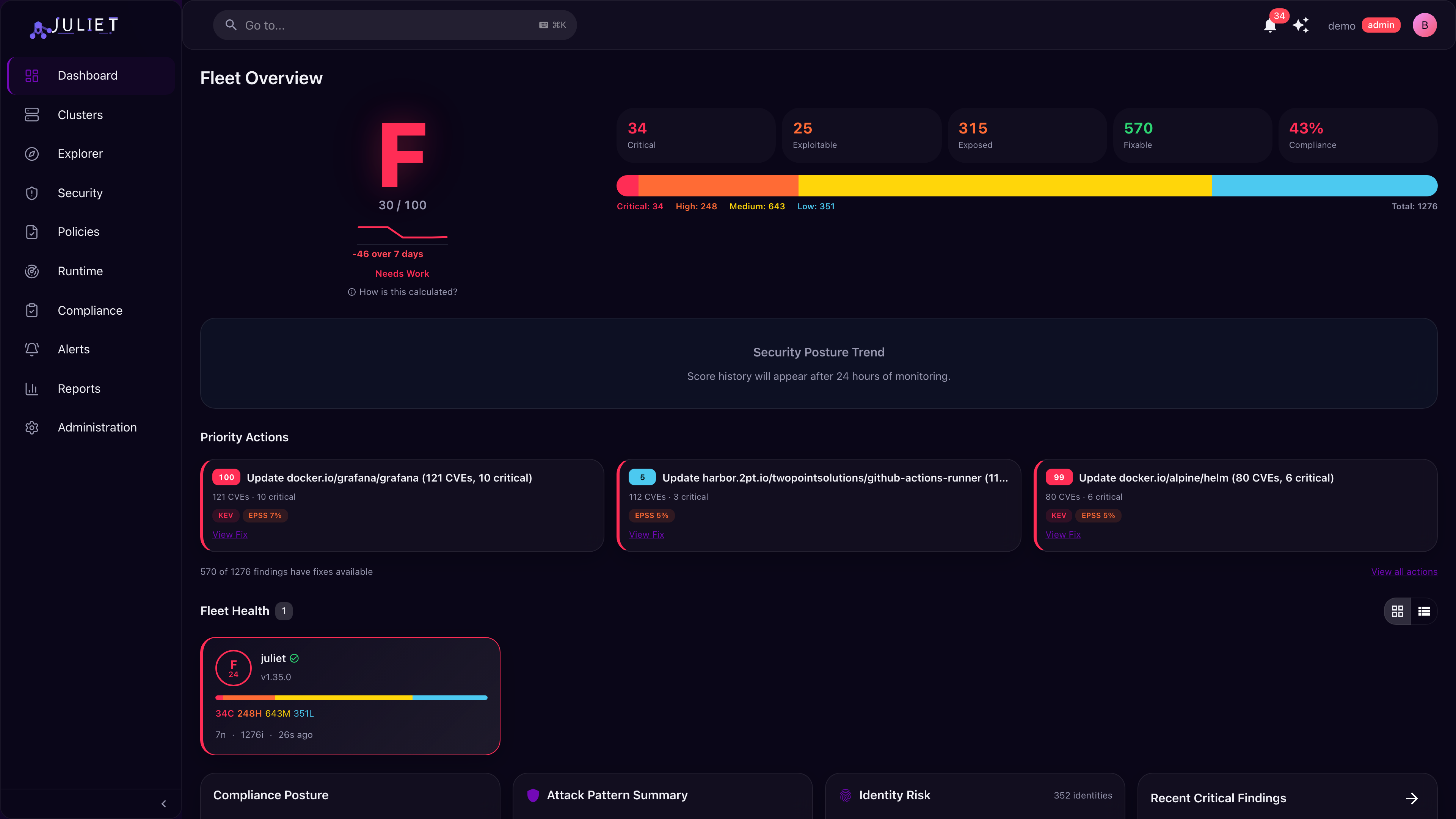
Scanners Give You Lists. Juliet Gives You Answers.
Traditional container security tools dump thousands of CVEs on your team with no context. Juliet automatically maps your entire Kubernetes environment as a connected graph. A KSPM approach that shows how resources relate to each other and which vulnerabilities are actually dangerous.
- Context, not just alerts. A medium-severity CVE on a pod with elevated permissions and internet exposure is actually critical. Juliet connects these dots automatically, with no manual investigation needed.
- Fix what matters first. Attack path analysis shows which vulnerabilities are actually reachable from outside your cluster, so your team stops chasing false priorities.
- See the full impact. When something is vulnerable, instantly see every workload and namespace in the potential impact zone, not just the single affected resource.
Deploy in Under 5 Minutes
One Helm chart. Zero infrastructure to manage. Full visibility.
Deploy Agents
One Helm chart deploys lightweight agents across your cluster. Minimal RBAC permissions, no privilege escalation, zero impact on running workloads.
Automatic Discovery
Juliet maps every resource, relationship, and vulnerability into a connected graph, automatically. No configuration, no tuning, no query language to learn.
Find and Fix
See exactly what's exposed, why it matters, and who should fix it. Actionable results from day one, not a backlog of unranked alerts.
See How Attackers Actually Get In
Not just a list of CVEs — Juliet traces the exact chain an attacker would follow from internet exposure to your most sensitive assets. Every path is verified, risk-scored, and comes with specific remediation steps.
- Verified attack chains — see the exact hop-by-hop path from entry to target
- One-click fixes — "Add a NetworkPolicy" breaks 16 of 20 attack paths
- Risk scoring — prioritize by real-world exploitability, not just CVSS
Ask Questions in Plain English
"Show me pods running as root with critical CVEs" — type what you're looking for and get instant results. Juliet translates natural language into multi-hop graph queries across your entire fleet.
- Natural language queries — no query language to learn
- Multi-hop traversals — Pod → Container → Image → CVE in one query
- Pre-built quick queries — one click to find privileged containers, exposed services, and more
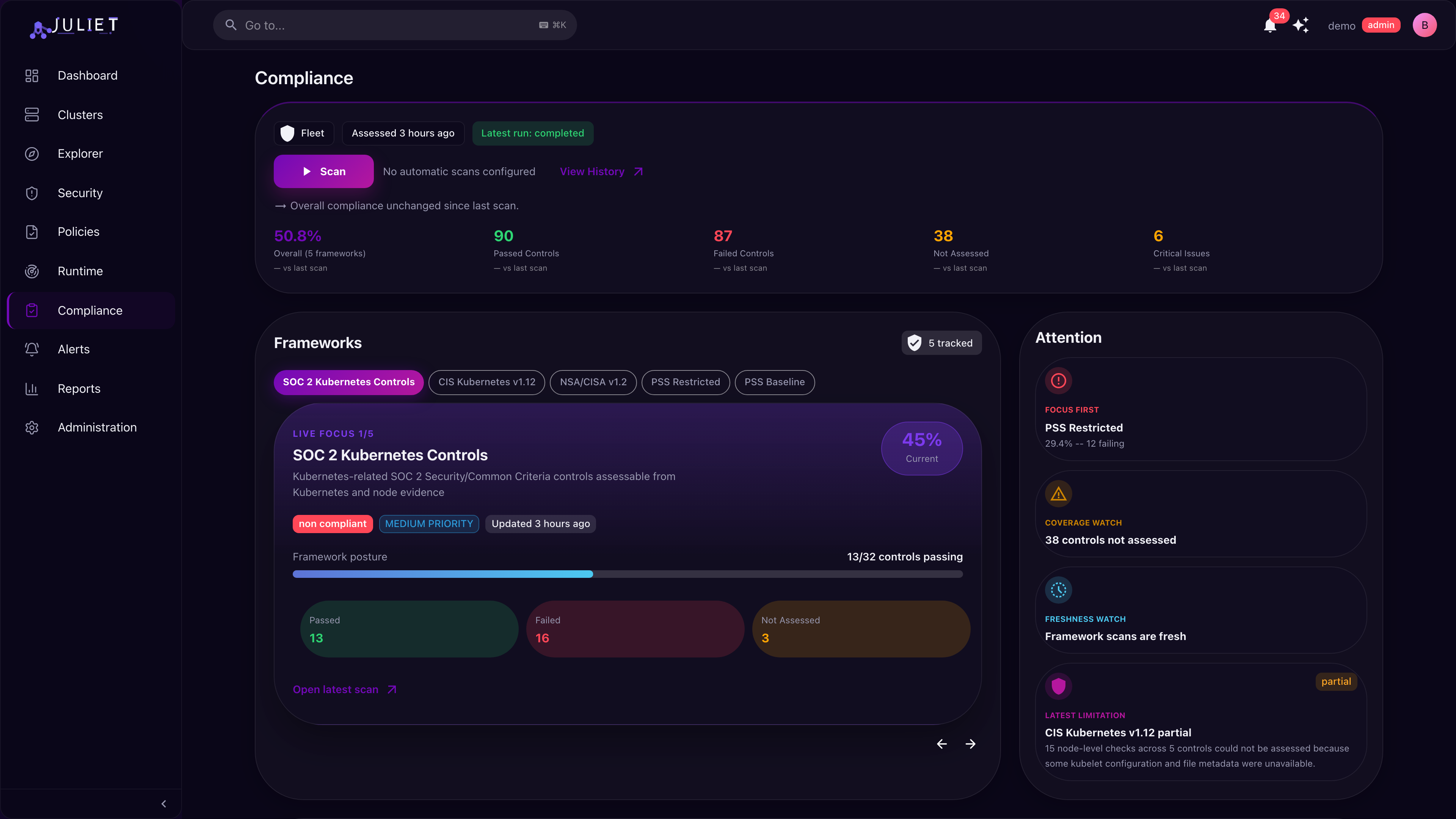
Continuous Compliance, Not Checklists
Measure your clusters against CIS Benchmarks, NSA/CISA, SOC 2, PSS, and PCI DSS — continuously. One-click scans with clear pass/fail results and framework-specific remediation guidance.
- Multiple frameworks tracked simultaneously with live posture scores
- One-click scanning — scans run server-side, no extra pods to deploy
- Attention alerts — instantly see which framework needs focus
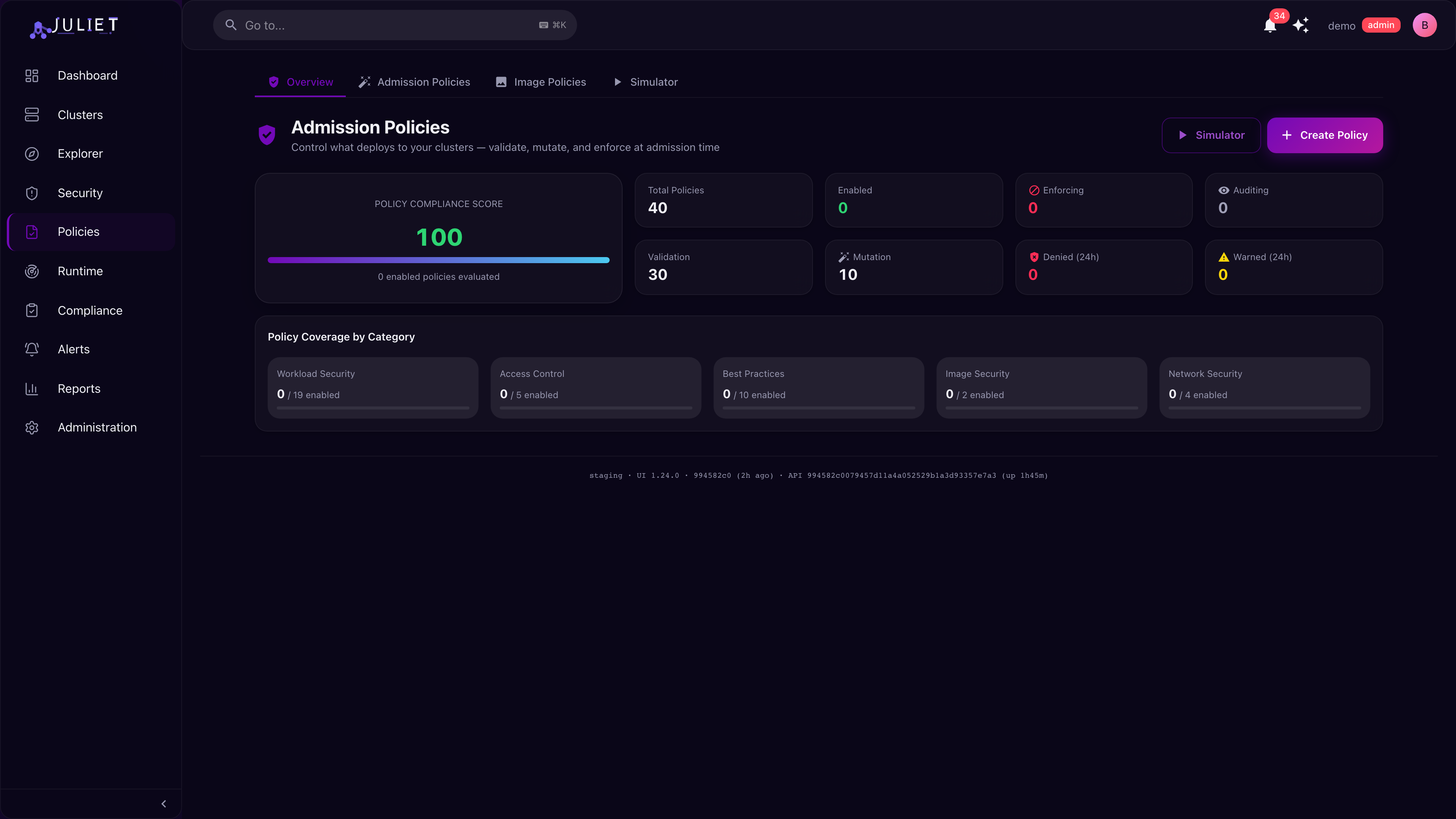
Stop Bad Deploys Before They Land
40 built-in security policies that block misconfigurations at deploy time. Enforce, audit, or warn — test against existing workloads before turning policies on. Includes a simulator to preview impact.
- Validate, mutate, enforce — choose your enforcement level per policy
- Policy simulator — preview what would be blocked before enabling
- 5 categories — workload security, access control, best practices, image security, network
Kubernetes Security Posture Management. Complete Visibility.
From container vulnerability scanning to runtime detection, everything you need to secure Kubernetes, without the tool sprawl. One CNAPP for your entire fleet.
Attack Path Analysis
See exactly how an attacker could move through your cluster, from internet exposure to privilege escalation to sensitive data. Prioritize remediation by real-world exploitability, not just CVSS scores.
AI-Powered Explorer
Ask questions about your security posture in plain English. Juliet translates natural language into multi-hop graph queries, finding exactly what you need across clusters, namespaces, and resources.
Vulnerability Management
Scan every container image for CVEs with SBOM-based analysis. Group by image, package, or namespace. Filter by severity, exploitability, and whether a fix is available.
Runtime Security
Detect threats as they happen with eBPF-based runtime sensors. Monitor process execution, network connections, and file access across your fleet with real-time event streaming and configurable policies.
Admission Control
Stop misconfigurations before they deploy. Fifteen built-in security policies plus custom Rego rules, with enforce, audit, and warn modes. Test policies against existing workloads before turning them on.
SBOM & Supply Chain
Full software bill of materials for every container image. Track packages, licenses, and known vulnerabilities across your fleet. Export in CycloneDX format for supply chain audits.
Compliance Frameworks
Continuously measure your clusters against CIS Benchmarks, EKS CIS, NSA/CISA, Pod Security Standards, PCI DSS, and more. Always-on monitoring with clear pass/fail results.
Identity & RBAC Analysis
Find over-permissioned service accounts, detect lateral movement paths, and spot RBAC misconfigurations. Risk-score every identity and prioritize by actual exposure.
Multi-Cluster Management
Connect EKS, GKE, AKS, and self-managed clusters into a single view. Compare security posture across environments, track drift, and manage everything from one dashboard.
Enterprise Ready
Built for organizations that need security, compliance, and control at scale.
Single Sign-On
Google OAuth integration for seamless team access. No separate credentials to manage.
Multi-Factor Authentication
TOTP-based MFA with recovery codes for every account. Enforce across your organization.
Full Audit Trail
Every action logged and searchable. User management with admin, developer, and viewer roles.
Multi-Tenant Isolation
Every customer gets a dedicated graph database. Complete data isolation at every layer.
Alerts & Reporting
Route alerts to Slack, Teams, PagerDuty, or email. Generate PDF security reports with letter-grade scoring.
API & Automation
Scoped API keys with read, write, and admin permissions. Full REST API for integrating with your toolchain.
Built with Security First
We built Juliet with the same rigor we expect from the infrastructure it protects.
- Per-customer data isolation with dedicated graph databases
- SSO and multi-factor authentication for every account
- Agent credentials scoped to minimum permissions with key rotation
- Full audit trail of every action for compliance reviews
- Enterprise-grade backup and retention with legal hold support
- Always-on health monitoring across all customer environments
Continuous monitoring against:
Get Started
Deploy Juliet in your cluster and see your security posture in minutes. One Helm chart, full visibility. No credit card required.
Already have an account? Sign in